IoT devices, part of the broader Internet of Things, are now everywhere, from modern office buildings to corner shops. IoTs are rapidly being deployed across strategic economic sectors such as energy, transport, agriculture, infrastructure, manufacturing, mining, and smart offices—at an unprecedented pace. The potential is immense and, from our point of view, still largely untapped, especially in the realm of cybersecurity and various emerging use cases.
Today, there are over 7 billion connected objects around the globe (sources noted at the end of the article), and that number continues to grow exponentially. This surge in adoption brings undeniable operational benefits—but also introduces a new layer of complexity. The more devices that connect, the larger the attack surface becomes. As a result, businesses of all sizes are increasingly exposed to vulnerabilities and security risks.
The reality is simple: IoT devices are being deployed faster than they can be secured. Many are designed with limited built-in protection, minimal update mechanisms, and inconsistent security standards. This is why we strongly believe that establishing a clear, scalable IoT network security framework is no longer optional—it is essential for modern enterprises.
In this series of articles, we share our vision and why we believe IoT network segmentation is a solution to explore, if not the answer.
What makes enterprise networks vulnerable
The proliferation of uncontrolled, unsecured devices, sensors, and third-party components is transforming corporate networks into highly complex ecosystems. Nowhere is this more visible—or more critical—than within Wi-Fi infrastructure and LAN environments that still rely on outdated segmentation models.
Many enterprises continue to depend on VLANs (Virtual Local Area Networks) to group devices and users. While VLANs were once effective, they were not designed for today’s scale or diversity of connected devices. In practice, VLANs often create large, flat network segments where devices can freely communicate with one another.
This lack of granular control and effective access control creates significant risk. Within a VLAN, lateral movement is typically unrestricted—meaning that if one device is compromised, the threat can quickly spread across the entire segment.
An open LAN environment, especially one that continuously accepts new devices, becomes a breeding ground for cyber threats. Malware and ransomware thrive in these conditions, exploiting weak points and propagating rapidly. Without the ability to strictly control traffic flows, networks become increasingly difficult to defend.
At the same time, enterprises face mounting pressure to onboard and manage an ever-growing number of devices—often with limited IT resources, making automation increasingly critical. The challenge is not just security, but scalability: how do you secure what you can barely track?
And this trend is only accelerating.
Why traditional approaches fall short
Legacy security models were built around users and endpoints—not billions of autonomous devices. Firewalls and perimeter defenses alone are no longer sufficient in a world where threats can originate from within the network itself.
IoT devices often operate silently in the background, making them harder to monitor. Many lack visibility tools, and some cannot even support traditional security agents. This creates blind spots—areas of the network where threats can exist undetected.
Additionally, IoT ecosystems are highly heterogeneous. Different vendors, protocols, and configurations make standardization difficult, further complicating security enforcement.
In this context, relying solely on network-level grouping (like VLANs) is no longer enough. What’s needed is a more dynamic, device-centric approach.
Is IoT network segmentation the solution?
There is good news. Despite sharing the same corporate infrastructure, IoT devices do not inherently need to communicate with one another. In fact, in most cases, they shouldn’t.
The vast majority of IoT devices are designed for a specific function: sending data to a cloud service, receiving commands, or interacting with a limited set of applications, thereby generating specific patterns of network traffic. This makes them ideal candidates for isolation.
By segmenting IoT devices at an individual level, organizations can drastically reduce risk. Each device can be placed in its own controlled environment, where its communication is restricted to only what is strictly necessary.
This approach offers several advantages:
- Reduced attack surface: Compromised devices cannot easily infect others
- Improved visibility: Traffic patterns become easier to monitor and analyze
- Granular control: Policies can be tailored per device, not per group
- Simplified compliance: Security rules are consistently enforced
Modern LAN segmentation solutions enable this level of control. They allow organizations to isolate devices, enforce policy-based communication, and direct traffic securely—whether to cloud platforms or on-premise systems.
Instead of managing networks as large, flat environments, IT teams can adopt a microsegmentation model that aligns with Zero Trust principles: never trust, always verify.
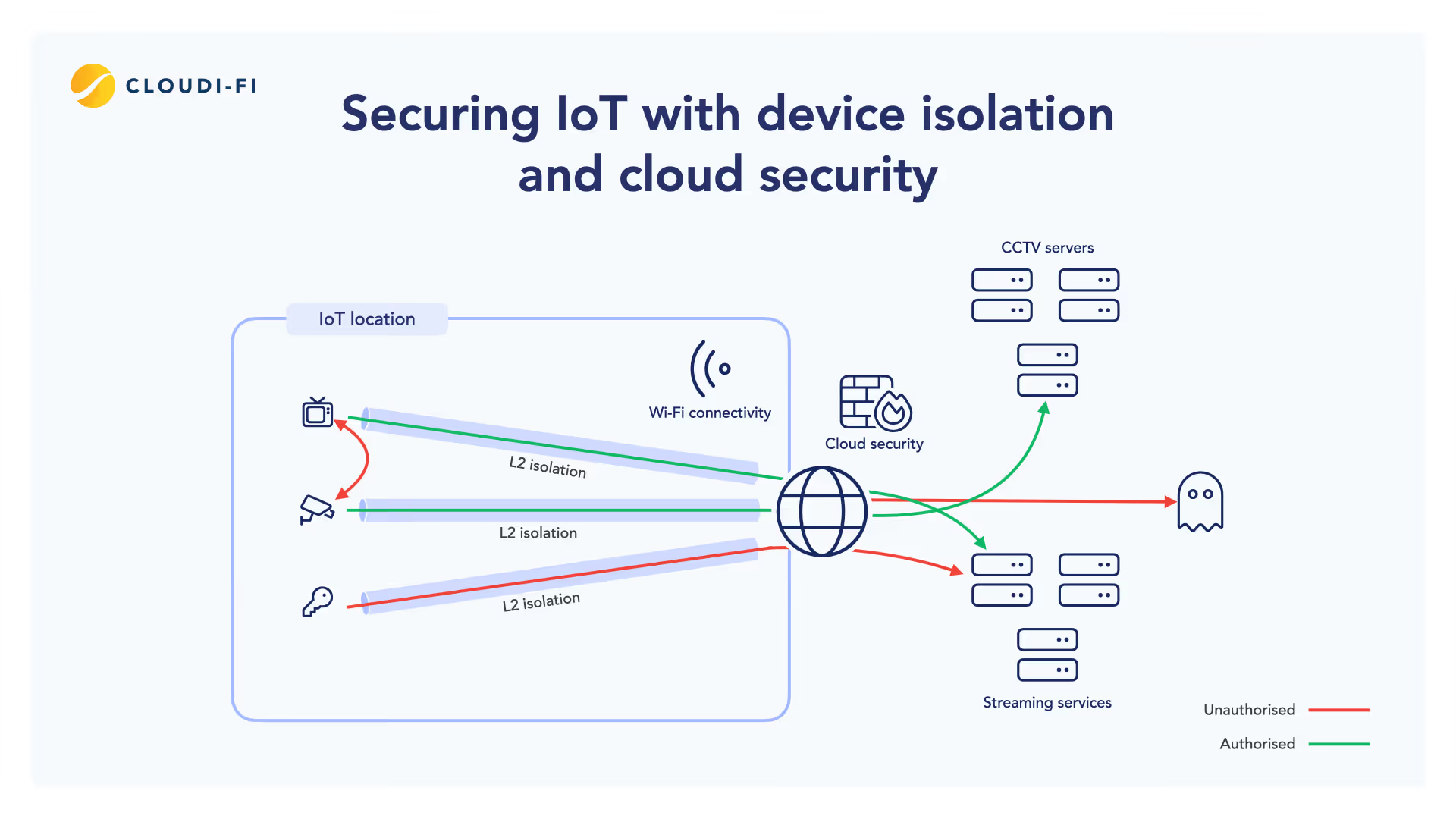
Securing IoT devices with isolation and cloud-based security
Open-segment LAN environments are no longer sustainable. They expose enterprises, users, and the IoT ecosystem itself to unnecessary risk.
To build resilient networks, organizations must rethink how devices connect, communicate, and are monitored.
Device isolation plays a critical role in this transformation. By ensuring that each IoT device operates within a controlled boundary, businesses can contain threats before they spread. Combined with cloud-based security inspection and policy enforcement, this creates a layered defense model that is both scalable and adaptive.
Traffic can be continuously analyzed, anomalies detected in real time, and policies dynamically updated—without disrupting operations or consuming excessive bandwidth.
IoT’s weakest link: A valuable target for hackers
Cyberthreats rarely begin at the infrastructure level—they start with people.
Ransomware and malware are designed to exploit human behavior. Phishing emails, social engineering tactics, and deceptive interfaces remain some of the most effective attack vectors. These methods are constantly evolving, becoming more sophisticated and harder to detect.
Once inside the network, attackers look for the weakest link—and IoT devices often fit that description.
Many IoT devices lack strong authentication, run outdated firmware, or cannot be easily patched. This makes them attractive entry points or amplification tools for larger attacks.
If a compromised device exists within an open network segment, it can quickly become a launchpad for lateral movement, data exfiltration, or service disruption.
Given enough time, an unsecured network will be breached. The question is not if, but when—and how far the attack can spread once inside.
Building a more resilient IoT future
Large enterprise networks have countless entry points, each representing a potential gateway for cyberattacks. As IoT adoption continues to grow, so does the urgency to address these risks proactively.
In this series of blog posts, our objective is to explore these vulnerabilities in depth and examine practical, scalable solutions. We aim to contribute to an ongoing industry conversation—one that brings together technology partners, customers, and security experts.
We firmly believe that structured IoT network segmentation, combined with clearly defined security frameworks, will play a key role in shaping the future of enterprise connectivity.
As we continue to design and build tomorrow’s IoT security management platform, your perspective matters.
Sources: https://explodingtopics.com/blog/iot-stats